信息收集小技巧
分享一个最近公司大佬教的信息收集技巧感觉挺不错的,适合用于大型企业,护网信息收集
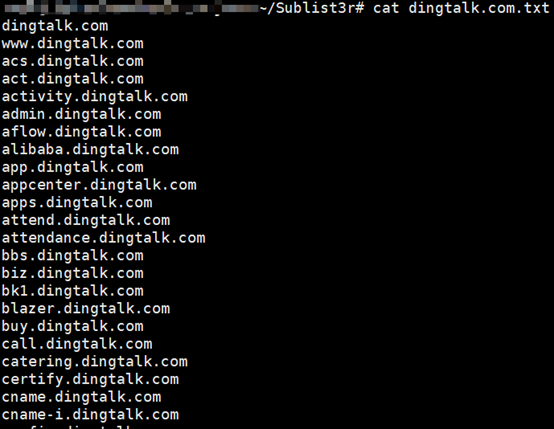
子域名收集
使用Sublist3r进行枚举枚举子域名
python sublist3r.py -d dingtalk.com -b -t 50 -o dingtalk.com.txt
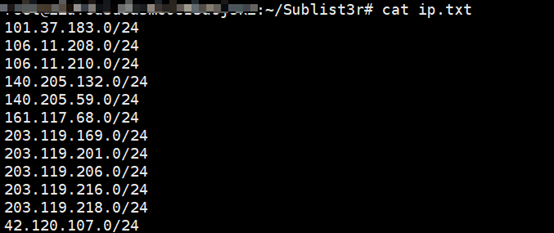
Ip段资产收集
使用BASH脚本把域名解析成IP,并且去重加C段识别
for i in `cat dingtalk.com.txt`;do host $i|grep -E -o "([0-9]{1,3}[\.]){3}[0-9]{1,3}";done >ips.txt

cat ips.txt |sort|uniq|grep -E -o "([0-9]{1,3}[\.]){3}"|uniq -c|awk '{if($1>=2)print $2"0/24"}' > ip.txt
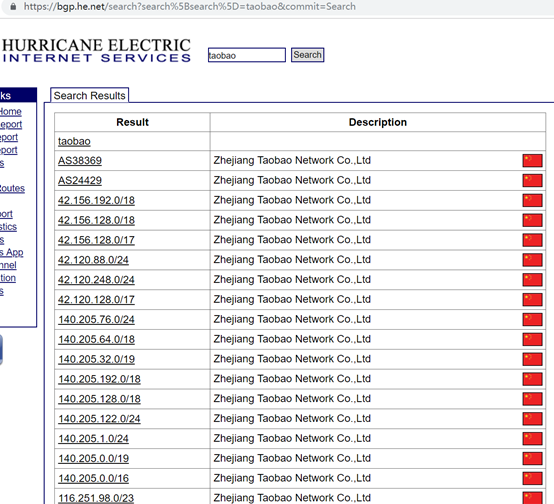
对于大公司的IP段的信息收集可以使用https://bgp.he.net
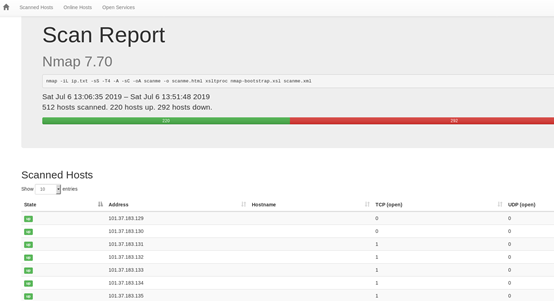
利用前面获取到的IP段,可以用nmap,masscan进行端口扫描,这里用到了一个nmap的的模板nmap-bootstrap.xsl,这个模板需要自行下载:https://raw.githubusercontent.com/honze-net/nmap-bootstrap-xsl/master/nmap-bootstrap.xsl
nmap -iL ip.txt -sS -T4 -A -sC -oA scanme xsltproc -o scanme.html nmap-bootstrap.xsl scanme.xml
(扫描完打开scanme.html文件可能会是xml格式的,使用xsltproc -o scanme.html nmap-bootstrap.xsl scanme.xml进行转换)
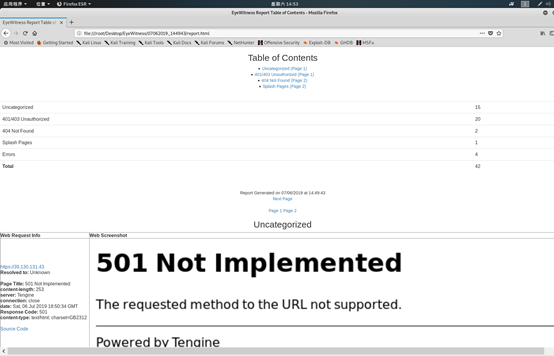
WEB资产识别
WEB资产识别,使用EyeWitness https://github.com/FortyNorthSecurity/EyeWitness
python EyeWitness.py -f 目标.txt –web –active-scan –add-http-ports 80,81,88,443,888,2082,2083,3122,4848,6588,7000,7001,7002,7003,8000,8080,8081,8089,8090,8443,8500,8888,9000,9001,9200,9043,9080,10000,10051,50000 –addhttps-ports 443,8443,9043
nmap -T4 -iL 目标.txt -oX scan.xml -p 80,81,88,443,888,2082,2083,3122,4848,6588,7000,7001,7002,7003,8000,8080,8081,8089,8090,8443,8500,8888,9000,9001,9200,9043,9080,10000,10051,50000 -Pn --open -n
python EyeWitness.py -x scan.xml --web --no-dns --active-scan